Beyond the Guest: Why the Control Plane is the New Front Line
Beyond the Guest: Why the Control Plane is the New Front Line
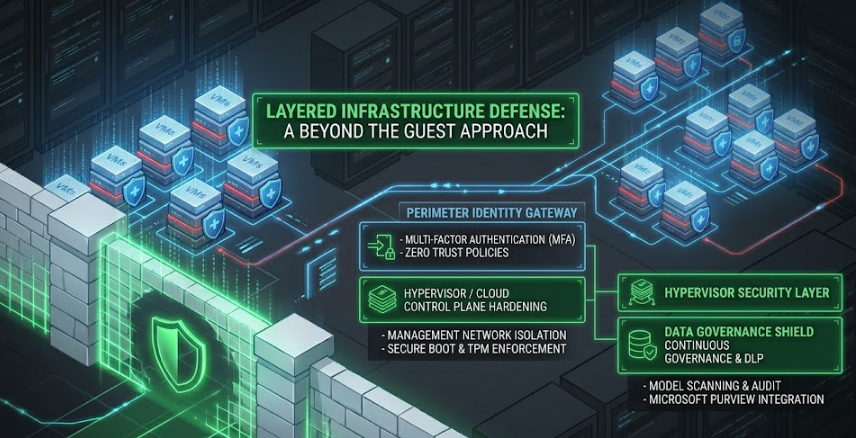
For the last decade, the mantra of the Blue Team has been "Harden the Host." We’ve spent countless hours patching Windows kernels, fine-tuning EDR agents, and chasing malware samples inside the Virtual Machine (VM). But as we move through 2026, the battleground has shifted.
The Guest OS is no longer the primary target—it’s just the consolation prize. Modern attackers aren't picking the lock on the hotel room door; they are stealing the master keys from the concierge. They are going after the Hypervisor and the Cloud Control Plane.
The "Eggshell" Security Problem
Traditional security is often like an egg: a hard outer shell (the firewall) and a soft, gooey center (the internal network). We’ve gotten better at hardening the "rooms" (VMs) inside that center, but we’ve left the "hallways" (the virtualization layer) vulnerable.In early 2026, we’ve seen a massive surge in ransomware variants specifically designed to execute at the hypervisor level. Why fight an EDR agent inside a Guest OS when you can simply encrypt the .vmdk or .vhdx files from the outside? If you control the hypervisor, the Guest OS is already dead—it just doesn't know it yet.
1. The "Silent" Entry: Identity is the New Perimeter
The most dangerous breach of 2026 doesn't start with a "Zero-Day" exploit. It starts with a stale access key or an over-privileged service account.In the cloud, the "Control Plane" is the set of APIs that manage your resources. If an attacker compromises a developer's identity that has FullAccess to an environment, they don't need malware. They can use legitimate administrative tools to:
- Create "Public" snapshots of private databases.
- Spin up massive GPU instances for crypto-jacking.
- Exfiltrate entire buckets of data (like the 149 million record leak we saw recently).
2. Hardening the Hypervisor: Infrastructure is the Target
If you are still running on-prem or hybrid virtualization, your ESXi or Hyper-V hosts are now high-value targets. Attackers are looking for unpatched management interfaces and weak API security.To defend the foundation, we have to move beyond just patching the Guest:
- Management Network Isolation: Your hypervisor management interfaces (vCenter, Prism, etc.) should never be routable from the general corporate network. It should be a "dark" network accessible only via a hardened jump box.
- Hardware Root of Trust: Enable UEFI Secure Boot and Virtual TPM. This ensures that the code running at the boot level hasn't been tampered with by a rootkit.
- API Token Governance: Treat your Cloud/Virtualization APIs as your most sensitive assets. Rotate keys frequently and monitor for "impossible travel" on API calls.
3. The 2026 Reality: Misconfiguration > Zero-Days
As a former System Engineer, I know the temptation to focus on the "cool" exploits. But the data doesn't lie: Misconfigurations cause more damage than Zero-Days.A Zero-Day is expensive for an attacker to buy or develop. A misconfigured S3 bucket or an "Allow All" Security Group is free. In 2026, "Continuous Security Posture Management" (CSPM) isn't just a buzzword—it’s a survival requirement.
For those of us working with tools like Microsoft Purview, this is where data labeling becomes a superpower. If you label your data at the source, your Data Loss Prevention (DLP) policies can catch it when an attacker—or a well-meaning admin—tries to move it into a "Public" cloud bucket.
Final Thoughts: The Architect's Mindset
The best security tool in 2026 isn't an AI-powered black box; it’s a clean, disciplined architecture.If the foundation—the hypervisor and the control plane—is solid, the attackers have nowhere to land. We need to stop thinking like "Room Cleaners" (checking VMs) and start thinking like "Building Architects" (securing the entire infrastructure).
Stay secure, stay curious.
— Sai Venkat Kaveti (cyberBROS)
0 Comments
No comments yet. Be the first to comment!
Leave a Comment